Ever opened a spam email? Not just fraudulent offers and wrong information, they can come with attachments. These attachments can contain malware, such as viruses, ransomware, or other malicious software. These attachments are designed to compromise the security of the recipient’s computer or network.
But what kind of attachments are actually harmful? Or are all of them harmful? Let’s talk about types of dangerous email attachments including:
- Executable Files (.exe, .bat, .msi): These files can contain malicious code that, when executed, can harm your computer or install unwanted applications to steal or compromise your data.
- Office Documents with Macros (.docm, .xlsm, .pptm): Malicious macros embedded in office documents can execute harmful actions on your system when the document is opened.
- ZIP or RAR Archives: While not inherently dangerous, these archive files can contain executable files or other malicious content. Some attackers use archives to disguise the true nature of the attached files.
- Links to Malicious Websites: While not an attachment per se, malicious links in emails can lead to phishing websites or sites that distribute malware.
However, these are still not that bad. There are still two types of attachments which are worse, ie, HTML and PDF files.
While we know what PDF files are, what exactly is an HTML file?
HTML (Hypertext Markup Language) is the standard markup language used to create and design documents on the World Wide Web. HTML attachments can potentially be dangerous if they contain malicious code. While HTML itself is not inherently harmful, it can be used to embed scripts, links, or other elements that execute malicious actions when opened.
Here are reasons why HTML and PDF attachments can pose a security risk:
HTML Files:
- Dynamic Content: HTML files can include dynamic content such as JavaScript, which may pose a higher risk if the code is malicious. This code can be changed by the spammer as it is dynamic and can lead to different types of results when clicked.
- Script Execution: since HTML allows the execution of scripts, it can be exploited for malicious purposes, leading to cross-site scripting (XSS) attacks. For example, someone could get access to your account and financial data.
- Phishing Attacks: such files can be used in phishing attacks to create realistic-looking forms and websites, attempting to trick users into providing sensitive information. For example, passwords and data.
- Exploitation of Vulnerabilities: scammers may attempt to exploit vulnerabilities in the browser or other software used to open them. Some HTML files could lead to unauthorized access, data breaches, or the execution of malicious code on the recipient’s system.
- Viruses: HTML attachments may include links or code that, when executed, initiates the download of malicious files. These files could be malware, ransomware, or other types of harmful software can could take over your device.
Now let’s talk about how PDF file attachments could be harmful:
PDF Files:
- Embedded Scripts: files can include JavaScript, potentially allowing for the execution of scripts. However, modern PDF viewers often have security features that restrict script execution.
- Malicious Actions: PDFs can contain links or actions that, when clicked, may lead to malicious websites or initiate downloads.
- Vulnerability Exploitation: Vulnerabilities in PDF viewers or the PDF format can be exploited to deliver malware or execute malicious code.
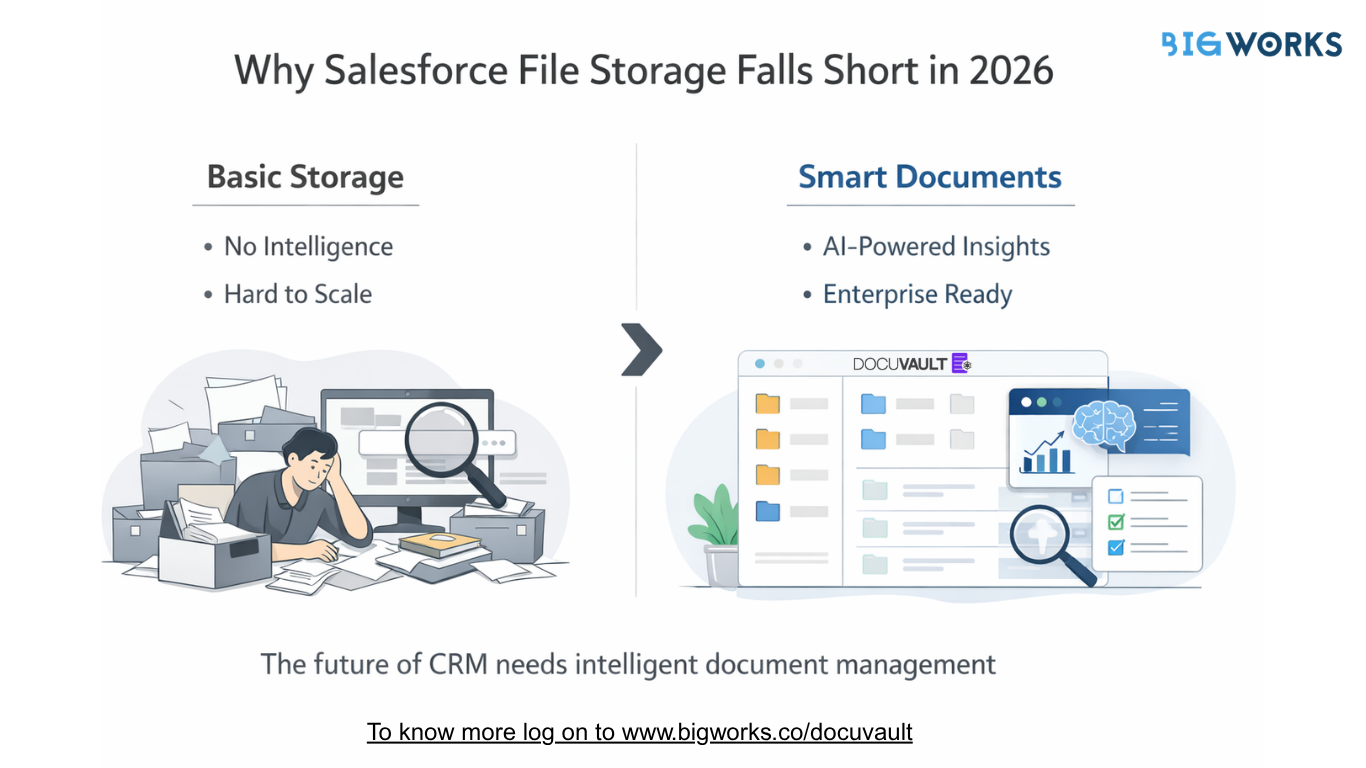
Now that we’ve gone over the risks, let’s see how we can mitigate them. Of course, don’t open attachments from unknown or untrusted sources. Verify the sender before downloading or clicking on any links. The other things you can do are:
- Get your hands on the right email client:
- Ensure that your email client and other software are up to date with the latest security patches to minimize risks. Configure your email client to disable the automatic execution of scripts or the rendering of HTML content in emails.
- Disable unnecessary features (like scripting) in your PDF viewer or browser to reduce potential attack vectors.
- Enable email filtering to automatically detect suspicious emails, reducing phishing attempts and malicious attachments reaching your inbox.
- Stay informed:
-
- Educate yourself about the risks associated with opening files from unknown sources and clicking on links within a file.
- Regularly backup your important data to an external, secure location. This ensures that even if you fall victim to ransomware or data corruption, you can recover your files.
3. Enable Two-Factor Authentication (2FA): Enable 2FA for your accounts to add an extra layer of security, making it more difficult for attackers to gain unauthorized access even if they manage to trick you into providing login credentials.
Now that we’ve discussed the risks and the solutions, it all boils down to the right emailing application. The ideal one will automatically scan your emails, filter them and ensure you never fall prey to any fraudulent emails or scams.
We suggest doing some research, looking into key benefits for your business and opting for an emailing app that keeps you safe from scams or dangerous attachments.