Whenever we think of data leaks we imagine masked hackers going through millions of lines of code, hacking a company’s secure infrastructure. However that is not the only way sensitive information is leaked, real life is far more boring, and in this article we’ll be going over different ways you can expose confidential information to the public.
Anytime an unauthorized user can access private or confidential data it is referred to as a data leak or data breach. However there is a subtle difference between the two.
What is a data leak?
A data leak refers to an unauthorized or accidental disclosure of information to unintended recipients. For example if an employee unintentionally sends confidential information to the wrong email.
A data breach on the other hand refers to a security incident in which unauthorized individuals hack systems or exploit security vulnerabilities and gain access to the information.
Overall the difference between a data leak and data breach is about intent. For data leaks the information is unintentionally exposed to a wider audience, but in a data breach, outsiders through deliberate actions exploit vulnerabilities with the intent of accessing unauthorized information.
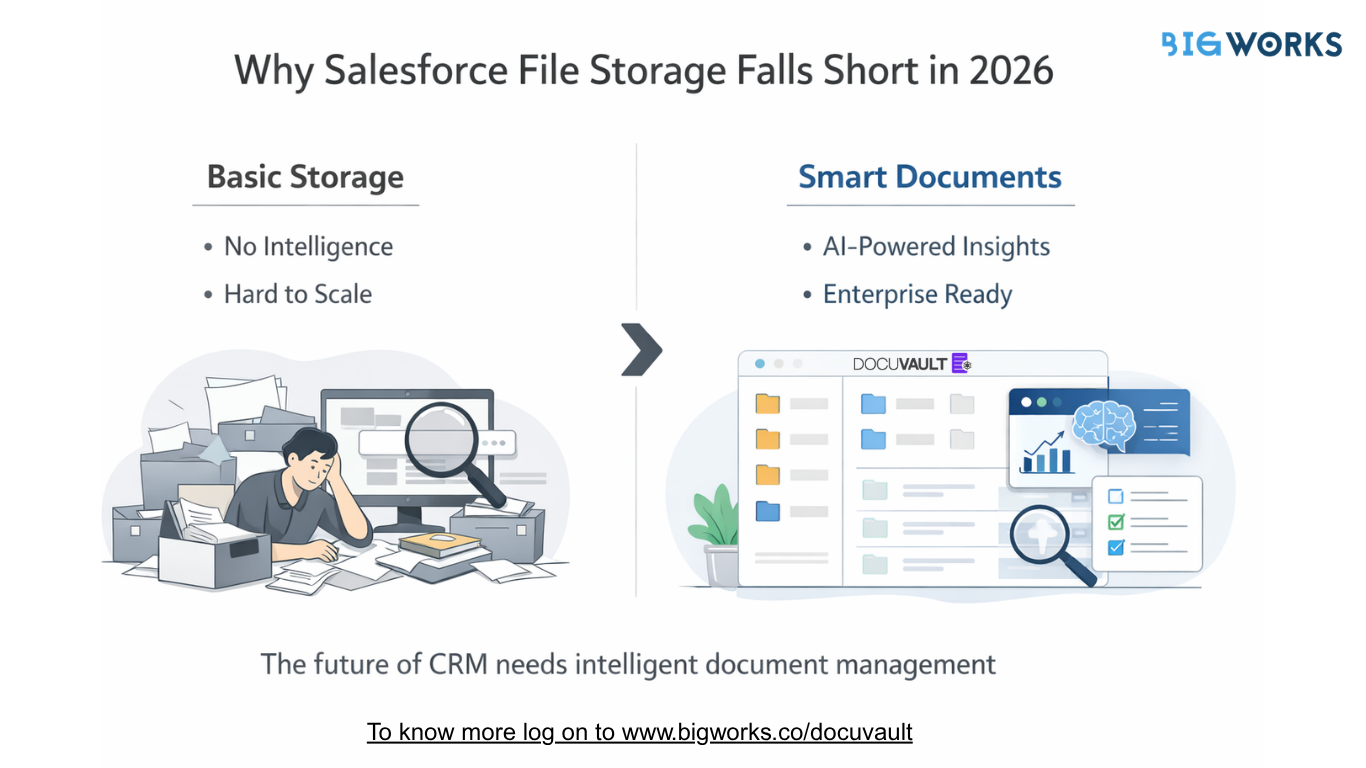
How can data leaks occur in CRMs
- Third-Party Integrations: Many CRM systems allow integration with third-party applications or services. If the security practices of these external integrations are not robust, it could potentially lead to a data leak.
- Phishing and Social Engineering: Attackers may employ tactics like phishing emails or social engineering techniques to trick CRM system users into divulging login credentials or other sensitive information. Once the attackers obtain valid credentials, they can gain unauthorised access to the CRM system and potentially extract or manipulate data.
- Misconfiguration: Improperly configured security settings in a CRM system can inadvertently expose sensitive data to unauthorised users.
- Accidental leak – Your employees send the wrong information to the wrong person.
How can you mitigate the risk of data leaks on your Salesforce CRM platform
Salesforce has implemented several measures to mitigate data leaks and enhance security on their CRM platform. Summarising the measures they have taken:
- Access controls and permissions.
- Two-factor authentication.
- Encryption of data in transit and at rest.
- Event monitoring and logging for detecting suspicious behaviour.
- Compliance with industry standards and regulations.
- Provision of security education and resources.
Thus the data on your Salesforce platform is secure. However, organisations using Salesforce also have a responsibility to configure the system properly and implement additional security controls to further reduce the risk of data leaks.
To ensure you’re completely leak proof, it is vital to ensure:
- When sharing information to third parties, your data transmission is secure.
- Employees have access to the relevant information on a need-to-know basis
- You’re sending the right data to the right person.
How BigWorks can help you mitigate data leaks
- Following best practices in coding: BigWorks Follows the best practices in coding such as access control, password management, thread modelling, Error handling, System configuration and much more.
- User access permissions: According to Salesforce’s best practices for file access permissions, a salesforce admin can control file permissions for every user by using roles, profiles and sharing rules.
- Industry standard security protocol: At BigWorks, best practices in Web Service Integration are enabled with high level security standards.
- Encryption For products: All files and products in BigWorks are encrypted using a 256-bit AES server side encryption and follow the Salesforce best practices for file access permissions.
At BigWorks we design and implement projects by providing secure transmission, data leak safeguarding, and foolproof security measures, when it comes to yours and customer data.